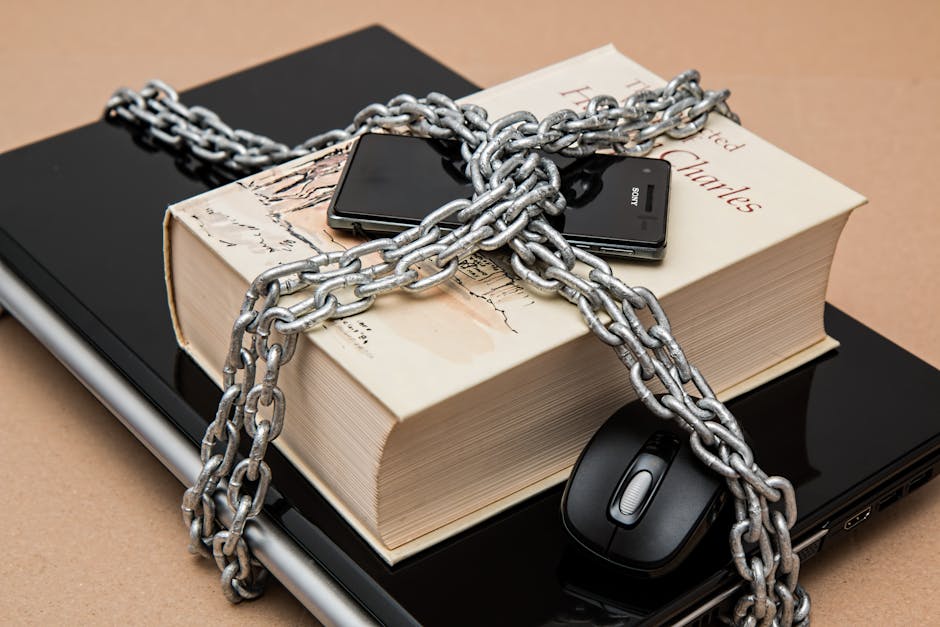
How To Secure Your Ssh Access On Linux And Windows
Why Default SSH Settings Are Risky
The default configuration of an SSH service often prioritizes convenience over security, which is exactly what attackers exploit. By default, many systems allow password-based authentication, which makes them vulnerable to credential stuffing and dictionary attacks where bots test thousands of common passwords per minute. Once an attacker finds a valid password, they have full access to your environment without needing any further verification.
Furthermore, allowing root login over SSH is a dangerous practice that gives an attacker immediate administrative control if they crack a password. This level of access enables them to install backdoors, steal sensitive data, or use your machine as a staging ground for further attacks. Moving away from these defaults is the first step toward a much safer remote management strategy.
Switch to SSH Keys to Secure Your SSH Access
The most effective way to eliminate password-related risks is to switch entirely to SSH key-based authentication. Instead of a password that can be guessed or stolen, you use a cryptographic key pair consisting of a private key, which stays securely on your local computer, and a public key, which you place on your remote server. The server verifies your identity by checking if you possess the corresponding private key, rendering brute-force password guessing completely ineffective.
Transitioning to keys adds a layer of complexity for attackers that is virtually impossible to overcome without stealing the actual physical private key file from your local machine. You can further increase this security by setting a strong passphrase on your private key, requiring you to enter it every time you connect. This means that even if someone manages to copy your private key file, they cannot use it without knowing your passphrase.
Generating and Managing Your SSH Key Pairs
Creating your own set of secure keys is straightforward on both Linux and Windows environments using built-in terminal tools. The standard command for generating these keys is ssh-keygen, which creates a highly secure Ed25519 or RSA key pair. After generating the keys, you must securely copy your public key to the target server, typically by appending it to the authorized_keys file.
Managing your keys properly is just as important as generating them, as you should never share your private key with anyone or store it in an insecure location. If you frequently connect to many servers, you should also consider using an SSH agent to hold your decrypted keys in memory. This setup prevents you from needing to type your passphrase constantly while keeping your keys safe on your disk.
Hardening the Configuration on Linux Servers
Once you have successfully transitioned to key-based authentication, you can make significant changes to the server configuration to further restrict access. You should modify the sshd_config file, which is typically found in the /etc/ssh directory, to enforce stricter security rules. This is where you disable password authentication, prevent root login, and restrict SSH access to specific users.
Additional hardening techniques include changing the default port from 22 to a non-standard port, which significantly reduces the noise from automated port scanners. While this is not a complete security solution, it filters out a vast majority of low-effort automated attacks. Ensure that you have tested your configuration before restarting the SSH service to avoid locking yourself out permanently.

Setting Up Robust SSH Protection on Windows
Modern Windows versions, including Windows 10 and 11, feature a built-in OpenSSH server that makes remote management seamless and secure. Enabling this service is easy through the Windows Features menu, and once activated, it works similarly to SSH on Linux. You can manage the service settings and configuration files in C:\ProgramData\ssh to apply the same security hardening principles.
Just like on Linux, the primary goal on Windows is to disable password authentication in favor of key-based access. You will place your public keys in the Administrators_authorized_keys file for administrative accounts or the authorized_keys file for standard user accounts. Properly setting the file permissions is critical on Windows to ensure that the SSH service trusts your key files.
Implementing Brute-Force Protection
Even with keys enabled, it is wise to add an extra layer of defense against automated attacks. Tools like Fail2Ban are designed to monitor your system logs for suspicious activity, such as repeated failed login attempts from a specific IP address. Once an attacker exceeds a predefined number of attempts, Fail2Ban automatically blocks their IP address via the system firewall.
This automated approach ensures that your system proactively protects itself without you needing to monitor logs manually. It effectively stops brute-force attacks in their tracks, saving system resources and preventing your logs from being flooded with malicious activity. Setting up Fail2Ban is a standard practice for any Linux server exposed to the internet.

Regular Maintenance and Updates
Security is not a one-time setup; it is a continuous process that involves keeping your software up to date. You should regularly check for security patches for the SSH service and apply them as soon as they are available to fix any newly discovered vulnerabilities. Relying on outdated software, even with good configuration, leaves your system open to known exploits.
A sound security strategy requires a holistic approach that goes beyond just configuration. Consider these essential maintenance tasks to keep your environment resilient over time.
- Keep your operating system and installed packages updated.
- Monitor your security logs for any unusual connection patterns.
- Use a trusted password manager to store your key passphrases.
- Audit your authorized_keys files periodically to remove stale keys.
- Consider using a VPN to restrict access to the SSH port entirely.