The Potential Impact Of Quantum Computing On Modern Military Encryption
Understanding the real impact of quantum computing on modern military encryption
The rapid evolution of quantum technology is fundamentally changing how we view data protection, especially regarding the significant impact of quantum computing on modern military encryption. Traditional security methods rely on complex mathematical problems that take classical computers millennia to solve. However, quantum machines operate on entirely different principles, threatening to break these foundations with ease.
Defense organizations rely on secrecy to maintain a strategic advantage, and the potential to decrypt historical data or intercept real-time communications keeps military strategists awake at night. This isn't a distant science fiction scenario but an emerging challenge that necessitates an immediate shift in security paradigms. Preparing for this shift is now a top-tier national security priority.
How quantum machines challenge current security standards
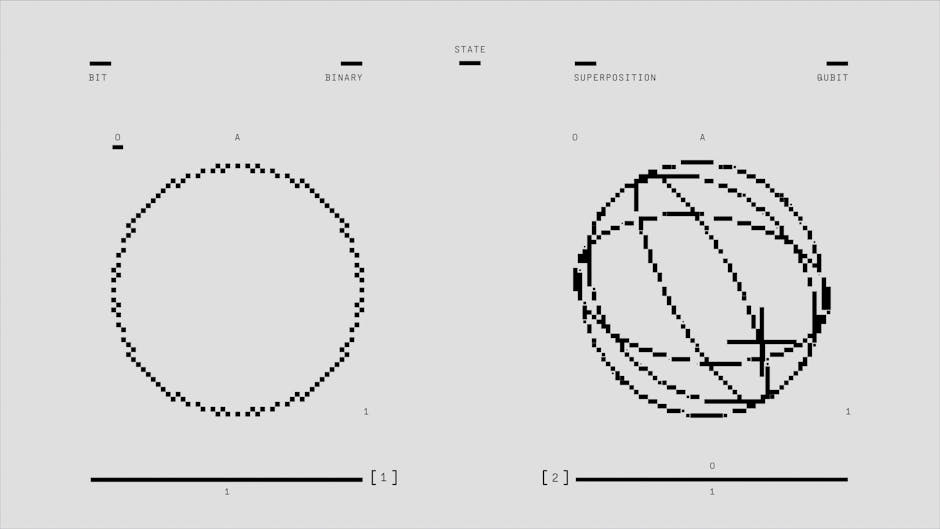
Classical computers work in bits, either zeros or ones, but quantum computers use qubits. This allows them to exist in multiple states simultaneously, enabling exponential processing power for specific types of calculations. This capability directly threatens the public-key infrastructure that protects everything from classified defense cables to sensitive intelligence databases.
Algorithms like RSA and ECC, which are standard for securing internet traffic and restricted networks, are particularly vulnerable. A sufficiently powerful quantum computer could factor large numbers or solve discrete logarithms in seconds. Once these mathematical barriers fall, the vast majority of existing encrypted data becomes accessible to anyone with the right hardware.

Why national security data is already vulnerable
There is a dangerous catch in the current landscape known as "store now, decrypt later." Adversaries may be capturing and storing encrypted military communications today, even if they cannot read them yet. Their hope is to hold onto this data until quantum technology matures enough to break the encryption in the future.
This means that information with a long shelf life, such as nuclear codes, strategic plans, or personnel identities, is already compromised. The damage is being done before the technology to cause it is even fully realized. Security professionals must treat data as if it were already public if it is protected by current, vulnerable standards.
The timeline for a post-quantum world
Experts debate exactly when a cryptographically relevant quantum computer will exist, but the consensus is that the timeline is narrowing. Developments in error correction and qubit stability are moving faster than many analysts predicted just a few years ago. While a fully fault-tolerant machine might still be a decade or more away, the window to transition is much shorter.
Waiting for the definitive breakthrough before acting is a recipe for disaster. The process of upgrading entire global military networks to quantum-resistant standards is a monumental logistical undertaking. Organizations must begin the migration now to stay ahead of the curve, rather than reacting to a sudden cryptographic crisis.

Strategies to safeguard sensitive information
Transitioning away from vulnerable systems requires a multifaceted approach that goes beyond just changing algorithms. Military organizations are exploring several robust strategies to ensure information remains secure during and after the transition. These approaches aim to make data unreadable even to advanced quantum attackers.
- Implementing quantum key distribution for creating unhackable communication channels based on the laws of physics.
- Adopting lattice-based cryptography which is believed to be resistant to quantum attacks.
- Updating software architectures to be crypto-agile, allowing for rapid swapping of algorithms as new threats emerge.
The race for quantum-resistant algorithms
The global security community is actively developing and standardizing new cryptographic methods designed to withstand quantum attacks. These post-quantum algorithms do not rely on the same mathematical vulnerabilities that quantum computers exploit. The goal is to create a new baseline that provides long-term security for critical infrastructure and classified communications.
Organizations like the National Institute of Standards and Technology are leading the effort to select and vet these new protocols. The challenge lies in balancing this new level of security with performance requirements, as military systems often need real-time, low-latency encryption. Finding the sweet spot between safety and operational efficiency remains the primary hurdle for engineers.
The new reality of digital defense
We are entering an era where digital safety is inextricably linked to the rapid advancement of quantum physics. Military branches that adapt quickly will maintain their strategic dominance, while those that linger on outdated systems will find themselves dangerously exposed. The shift is not just about technology but about a complete overhaul of how we define and implement security.
This transition will be costly, complex, and filled with technical challenges, yet it is unavoidable. Embracing a post-quantum mindset is the only path forward to protecting sovereignty and information integrity. The focus now is on building resilience before the digital landscape shifts underneath our feet.