How Mobile Game Anti-Cheat Systems Operate
Ever wonder why your favorite competitive game feels so fair, even when you are sure you are playing against someone who might have an unfair advantage? Behind the scenes, developers are constantly deploying complex tools to protect the integrity of every match. These mobile game anti-cheat systems are the unseen guardians working tirelessly to identify and neutralize malicious actors. They are essential for keeping gaming fun and competitive for everyone.
The Core Functions of Mobile Game Anti-Cheat Systems
These systems act as a multi-layered barrier between genuine players and those attempting to manipulate game data. At their heart, they are designed to detect discrepancies in how a game is being played compared to the intended rules. By monitoring both the player's device and the server data, these systems form a comprehensive defensive strategy.
Effective protection relies on a combination of signature scanning and behavior analysis. While simple methods look for known forbidden software, more advanced approaches watch for patterns that deviate from normal human inputs. This dual-layered strategy is crucial for keeping up with evolving cheating techniques.
How Client-Side Detection Monitors Your Device
The client-side component resides directly on your phone or tablet while the game is running. Its primary job is to inspect the environment for unauthorized modifications, such as modified game files or third-party applications intended to give an edge. If it detects something suspicious, it immediately reports the issue to the game server.
Because mobile devices have strict permission models, these tools must work within the constraints of the operating system. They frequently check the integrity of memory space to ensure the game code has not been tampered with. This constant vigilance helps prevent common techniques like speed hacks or unauthorized aim assistance tools.
Server-Side Analysis: The Final Arbiter of Truth
While the device can be compromised, the game server remains the ultimate authority on what happens in a match. Server-side analysis processes every action performed by players, comparing them against expected game mechanics. If a player suddenly teleported across the map or fired an impossible number of shots in a second, the server flags this anomaly instantly.
This approach is incredibly difficult for bad actors to bypass because they cannot directly modify the server logic. It focuses heavily on statistical analysis and heuristics to identify patterns typical of automated software or scripted behavior. By validating inputs at this level, developers can ensure that only legitimate game state changes are applied.
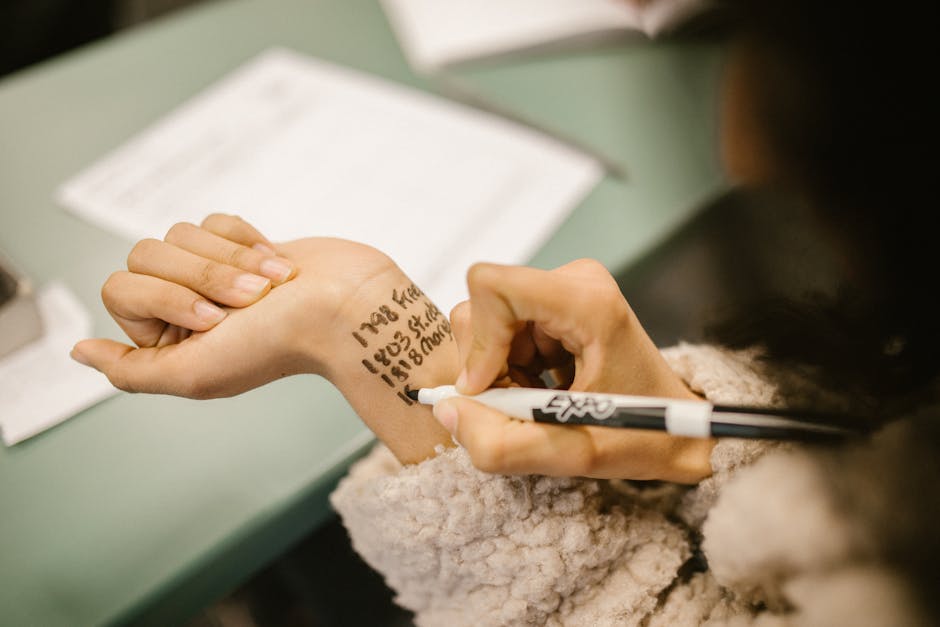
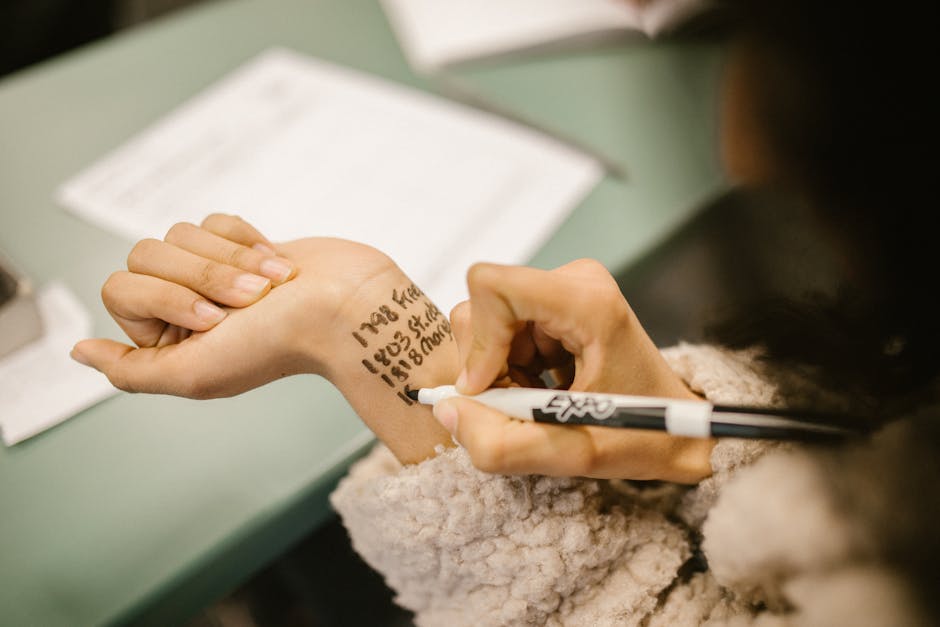
Identifying Malicious Software and Modified Files
Cheaters often use external tools to inject code or modify game assets, which is where specialized detection techniques come into play. These systems maintain a database of known threats and signatures of common cheating software. When the game launches, it performs a scan to see if any of these items are active or present on the device.
Advanced techniques go beyond static file checking to identify behavior typical of injected code. If the system detects that the game executable has been hooked or its memory modified, it takes action. The defensive response can range from a warning to a temporary suspension, or even a permanent ban for repeated offenses.
The Never-Ending Battle of Updates and Patches
The security landscape is constantly shifting, with new exploits emerging almost as quickly as developers can patch them. When a new game update is released, it often includes updated signatures and detection patterns to counter the latest threats. This cat-and-mouse dynamic is what keeps developers on their toes, forcing them to refine their defenses continuously.
Staying ahead requires a blend of automation and human intelligence to analyze new cheating methods. Developers monitor forums, community reports, and suspicious data patterns to understand how the newest exploits work. Once identified, they can push out server-side patches that immediately neutralize the new threat without requiring players to download a massive update.
Balancing Robust Security with Device Privacy
A common concern among players is how much data these systems actually collect and whether it impacts their privacy. Developers are typically very careful to ensure that monitoring is restricted solely to activity related to the game environment. The goal is to detect cheating, not to snoop on personal files or unrelated applications installed on the phone.
Modern approaches aim to be as lightweight and transparent as possible. Transparency is key to maintaining trust, and many studios provide details about their security measures. When implemented correctly, these protective layers should not significantly impact battery life or system performance.
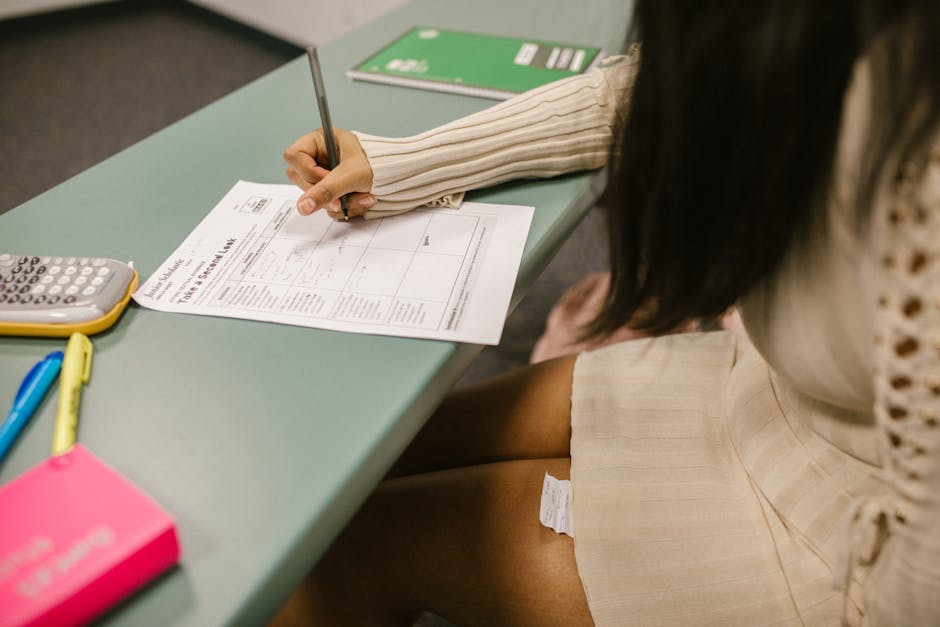
How Players Contribute to a Fair Environment
Players are often the first line of defense in identifying suspicious activity during live matches. Reporting players who seem to be using unfair advantages helps developers refine their detection systems by providing real-world examples to analyze. These reports act as invaluable data points that train and calibrate the automated detection mechanisms.
You can make a real difference in the community by following a few simple practices to keep the ecosystem clean. These proactive steps ensure that you are not accidentally contributing to vulnerabilities that bad actors might exploit.
- Use the in-game reporting tool immediately after suspecting unfair play.
- Avoid downloading or installing third-party apps that promise game currency or performance advantages.
- Keep your game and operating system updated to ensure the latest security patches are applied.
- Do not share your account credentials with anyone, as this increases the risk of your account being used for prohibited activities.
By staying vigilant and reporting suspicious behavior, you contribute to a better, more secure gaming experience for everyone. Your input combined with sophisticated automated systems creates a formidable barrier against those who refuse to play by the rules.